Leverage broad spectrum data protection capabilities beyond encryption to reduce PCI DSS audit scope and comply with the expanded data protection requirements.

Pseudonymize and Anonymize sensitive data for regulatory and industry standards compliance
Learn More
Enable data privacy with dynamic data masking and role-based access controls
Learn More
Control who can access sensitive data and to what degree; full, partial, or no access
Learn More
Implement & Automate Data Protection Policies to encrypt data at the application level
Learn MoreSecuring data anywhere it’s stored, moved, or used, EncryptRIGHT’s crypto-agile architecture abstracts the data protection functionality from the applications it protects. This enables organizations to seamlessly adapt to new regulatory mandates and operational demands, reducing development costs and future-proofing against evolving PCI DSS or any other regulatory changes.
EncryptRIGHT’s innovative functionality deploys in a single code base that integrates in as little as three lines of code, without needing developers to be security experts. Any application anywhere–on premises or in the cloud can simply:
Data is immediately secured or revealed in the exact manner for the authorized user defined in the policy.
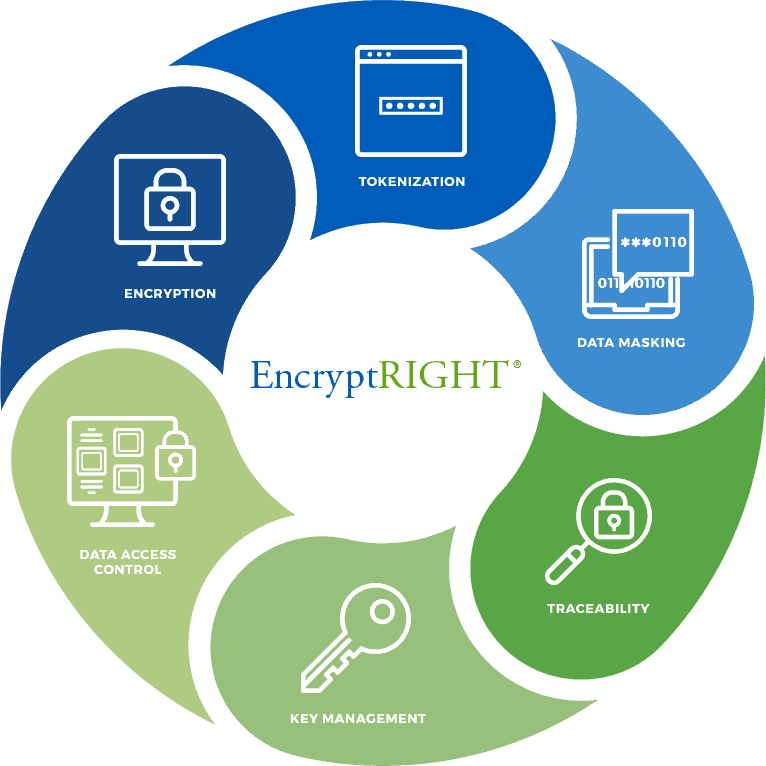
Leverage a variety of strong data security techniques in a single code base including encryption, tokenization, data masking and redaction, hashing, and signing to ensure confidentiality and integrity of data everywhere.
Simplify data protection at the application layer while facilitating compliance with the latest PCI DSS standards. Rather than interweaving cryptography, applications send a piece of data to EncryptRIGHT which secures or reveals it based on a defined policy.
Leverage the functionality of an embedded Enterprise Key Manager (EKM) for any data EncryptRIGHT protects to ensure critical keys are always secured and available when needed.
Streamline compliance with extensive audit logging and reporting functionality that supports external SIEM integration for traceability and verification that PCI auditors look for.
Define and enforce what data authorized users can secure, access, and reveal with granular role-based permissions that work seamlessly with built-in audit logging to help comply with PCI DSS.
Secure data in whatever environment(s) works for your business, on-premises, in the cloud, or across hybrid deployments. Reduce complexity with support for common operating systems and interfaces like COBOL, C#, Java, REST API and more.
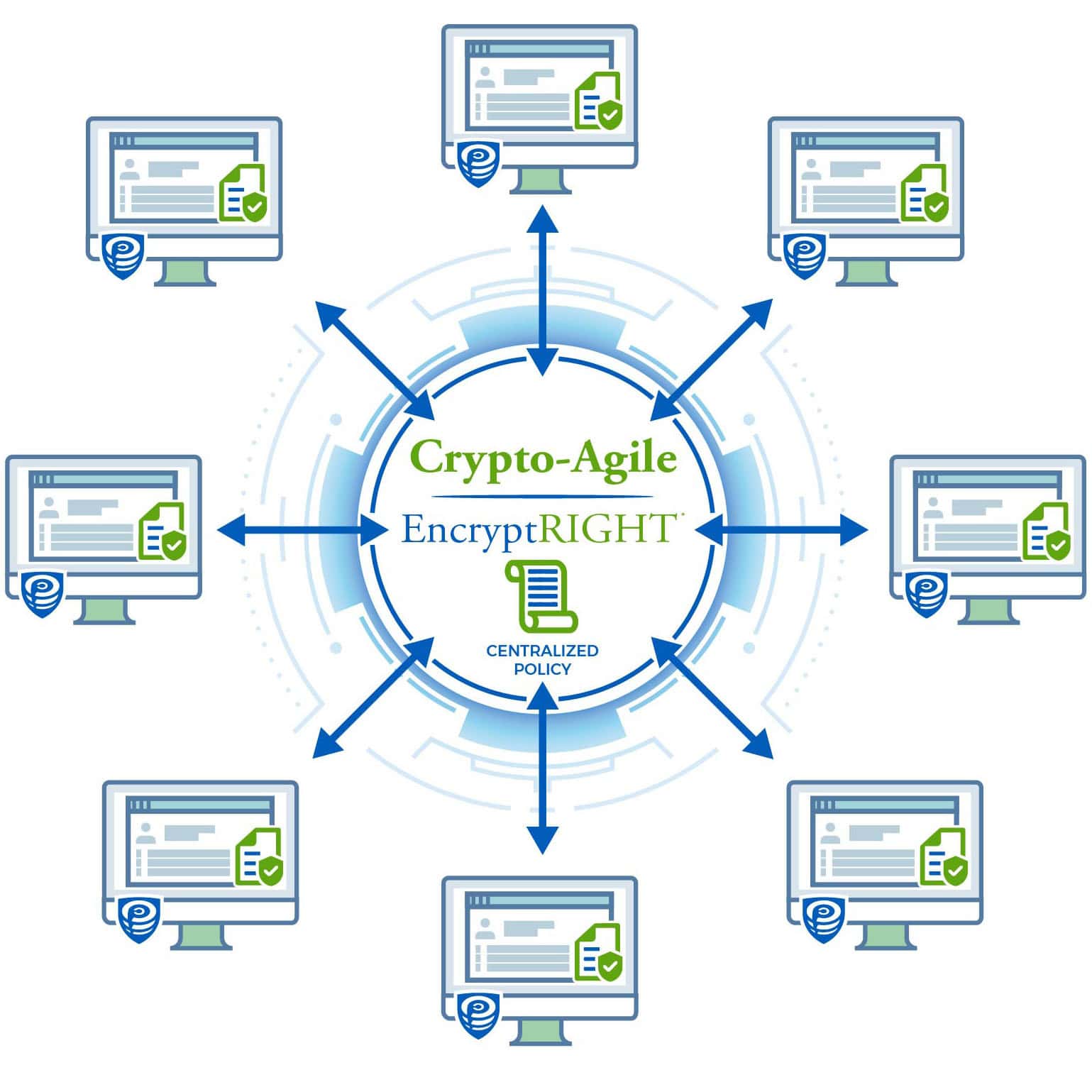
PCI DSS now requires documented plans to respond to cryptographic vulnerabilities and recommends crypto-agility as a best practice. EncrypRIGHT's crypto-agile architecture enables rapid adoption of stronger algorithms to stay ahead of evolving threats. It leverages a policy-driven approach that allows for centralized control and distributed enforcement of security. Any facet of security (algorithms, protection techniques, masks, or keys) can be swapped by making changes to a policy without application re-work.
A built-in data protection policy engine allows you to establish and enforce how data is protected, who may access the specific data, and what format that data will take when access is granted through dynamic masking (unrestricted, partially masked or fully restricted). Data protection policies are automatically and uniformly enforced, and built-in audit and reporting functionality provides traceability and alerting to assure that data is secured, privacy is protected, and compliance is met.