EncryptRIGHT includes a comprehensive, centralized encryption key management system for orchestrating all of the cryptographic keys related to data protection, including the ability to generate, exchange, distribute, store, rotate, temporarily suspend, revoke, and destroy cryptographic keys.
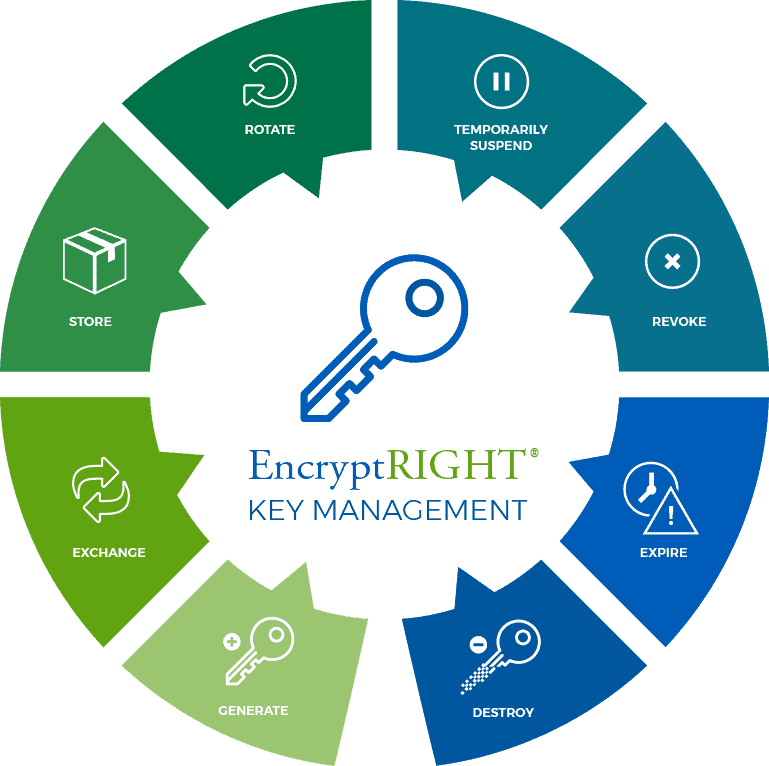
Key lifecycle can be managed by setting key status to currently active, to future effective key, or to expired. Expired keys can be kept and used for verifying authenticated or signed data and decryption, but they cannot be used to create new authentication codes, signatures or encrypt data. As needed, keys may be automatically deleted when expired or on a per-key configurable time afterwards.
Role-based access controls can be leveraged to identify what users have permission for key generation and maintenance, and all administrative actions are recorded in the audit log. EncryptRIGHT supports symmetric or asymmetric keys and allows multiple users to enter components for symmetric keys. EncryptRIGHT can be configured to require a quorum of users for encryption key management (as well as most other administrative functions).
EncryptRIGHT provides the ability to define automatic key rotation where new versions are created on a schedule. Keys may be automatically deleted once they are expired, kept forever for archiving purposes, or set to delete after they have been expired for a certain amount of time.
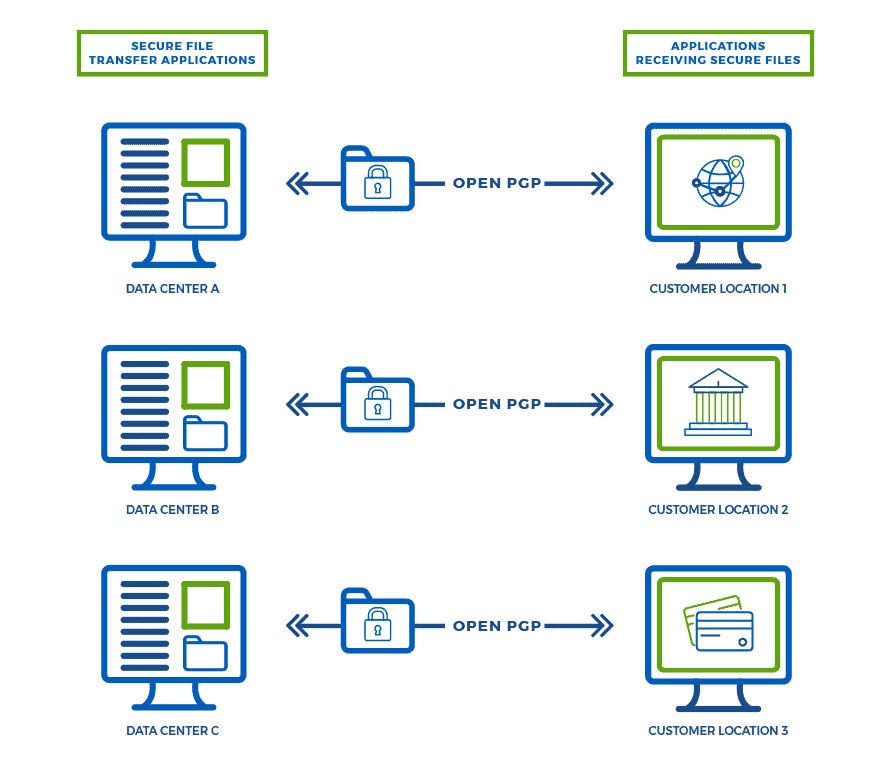
EncryptRIGHT includes support for OpenPGP standards to protect files for secure transfer facilitating the creation, management, and rotation of cryptographic keys related to OpenPGP.
It can also be configured as an PGP key server. When secure files are transferred out of the enterprise, EncryptRIGHT can securely serve PGP keys to outside recipients, allowing them to fetch the public keys required to unsecure the files.
For more information about the OpenPGP standard, refer to:
https://www.openpgp.org/about/standard/
The Key Management Interoperability Protocol (KMIP) is a protocol created by the Organization for the Advancement of Structured Information Standards (OASIS). The purpose of KMIP is to facilitate a standard method of exchanging cryptographic keys and other information between systems. EncryptRIGHT includes a KMIP server that allows KMIP clients to access, create and retrieve symmetric or asymmetric cryptographic keys.
For more information about the KMIP protocol, refer to the documentation provided by OASIS: https://www.oasis-open.org/committees/kmip/
