Managing Cryptographic Payment Keys can be very complex from both information security and developer standpoints. It requires specialized expertise to develop a payment key management system from scratch and replicate compliance requirements related to issuing payment credentials and processing payment transactions. But any initial effort to set up a system with proper payment key management is just the starting point. Payment Key management functionality must be constantly updated to keep up with the ever-evolving payment security landscape. It’s complex, but Prime Factors’ Bank Card Security System (BCSS) can help.
BCSS Payment Key Management has processes and workflows that meet payment key management requirements established by the standards bodies and the network brands, such as such as Visa, MasterCard, Discover, American Express, and JCB. BCSS Payment Key Management typically consists of four elements:
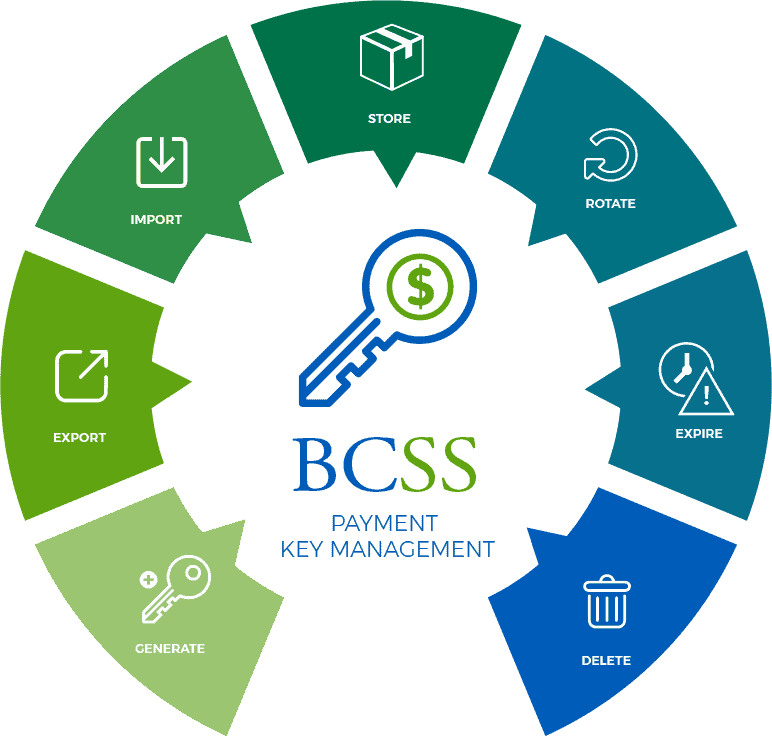
BCSS provides a library of subroutines that handle more than 100 functions that access the BCSS key vault database and a payment HSM. This makes it easier to securely generate, export, import, store, rotate, expire, and delete payment-specific cryptographic keys and EMV certificates.
Please note: Prime Factors is not a payment processor and does not offer payment processing services. Our customers can leverage Prime Factors software to help accelerate the development of their applications and secure their data, however, Prime Factors does not process, store, or otherwise access payment transactions or related data of our End Users.
